A lady strolls right into a grocery retailer, desirous about grabbing some apples. Earlier than she even reaches the produce aisle, a safety digicam has scanned her face. Whether or not the device is checking for shoplifters or just logging her arrival, her face has joined a virtual ledger, a hint she will’t simply erase. Shops, banks, airports, stadiums and place of work constructions are doing the similar.
However what if the girl’s facial knowledge is stolen or misused? If a cybercriminal steals her password, she will trade it. In the event that they achieve her bank card quantity, she will cancel the cardboard. However she will’t reset or revoke the illusion of her cheekbones.
Facial reputation techniques don’t stay exact pictures. They convert a face right into a mathematical template that maps the positions and proportions of the face’s options. When every other digicam scans an individual later, the device assessments their reside face towards those templates to substantiate an id.
In my paintings as a cybersecurity professor at Rochester Institute of Generation, I’ve discovered that despite the fact that templates are extra safe than footage – which someone on-line can seize and manipulate – templates, too, may also be stolen. As soon as that occurs, those virtual keys create a lifelong vulnerability. If a facial reputation database is breached, the “locks” {that a} template opens – gaining access to a financial institution app, getting via safety at an airport, coming into an place of work construction – can’t be reset. An individual’s face is everlasting, and so is the risk.
The risk isn’t theoretical. Biometric information has been stolen in information breaches. In 2024, biometric information from a facial reputation device used at bars and golf equipment in Australia was once hacked. And in 2019, biometric information from a pilot facial reputation device arrange by way of U.S. Customs and Border Coverage was once breached in an assault on a subcontractor’s community. It’s no longer transparent whether or not someone’s stolen biometric information has been exploited, alternatively.
Catching a ballgame? Safety cameras could be catching and digitizing your face.
AP Picture/Matt Slocum
Monitoring your face
All biometric identifiers raise dangers. Fingerprints and iris scans, alternatively, are usually utilized in managed eventualities, similar to unlocking an individual’s telephone or permitting anyone to go into a construction. In those instances, an individual has to intentionally take a look at a scanner. Cameras in public areas, against this, can seize faces as folks stroll by way of, from a distance and with out the folk whose faces are scanned understanding it.
If a fingerprint or iris database is breached, a thief nonetheless must bodily provide that finger or eye, or a pretend of it, to a scanner. On the other hand, anyone may fit a stolen facial template towards pictures from surveillance cameras or footage circulating on-line, making it more straightforward to spot an individual of passion or monitor anyone’s actions and actions.
There’s additionally a large distinction, technically and ethically, between maintaining a face on a telephone as opposed to handing it over to a database. On fashionable Apple gadgets and plenty of Android techniques, biometric information used to unencumber the gadgets is saved in the community in a devoted {hardware} chip and isn’t shared with the producer or cloud products and services for authentication. In consequence, a breach of company or cloud techniques would no longer disclose those device-level biometric templates.
Some side road and safety cameras in public are passive, simply gazing as folks go by way of, without a long-term information. However others is also following folks’s steps, linking faces to databases and making a continual virtual path. The danger rises when organizations use techniques to trace specific folks throughout more than one databases. Airport techniques may evaluate a traveler’s face towards passport or airline databases. Stadiums would possibly evaluate faces towards native safety watch lists or regulation enforcement lists. The corporate that manages Madison Sq. Lawn has used facial reputation to bar access to legal professionals at companies that represented individuals who sued the corporate.
Some huge retail chains, similar to Wegmans and Goal, additionally use facial reputation techniques of their robbery prevention efforts. Each and every new seize provides every other everlasting report.
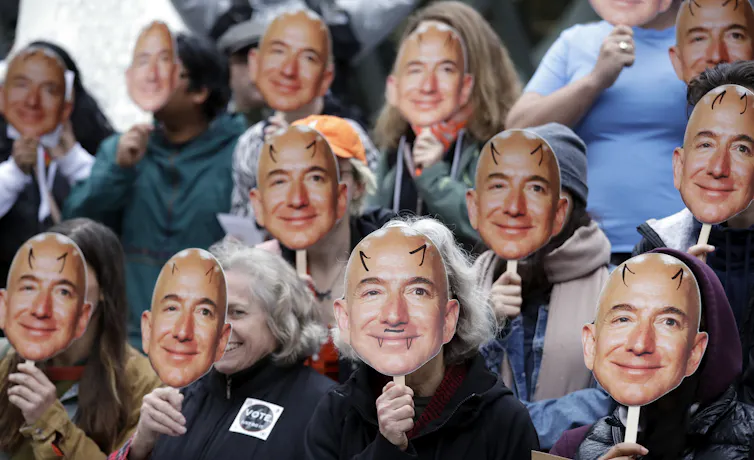
Demonstrators grasp pictures of Amazon CEO Jeff Bezos in entrance in their faces all through a protest over the corporate’s facial reputation device.
AP Picture/Elaine Thompson
Many corporations wouldn’t have experience in cybersecurity and depend on third-party distributors to regulate their information. If the ones centralized techniques are breached – or the datasets are connected throughout platforms, distributors or information agents – your face can grow to be a form of continual identifier, which can be utilized to reveal or monitor you. In some instances, when blended with different compromised information, your captured face can decrease the barrier to impersonating you.
When an individual’s face meets their information
And mixing a template with AI equipment similar to deepfakes or three-d face fashions may, in some instances, permit a legal to impersonate a person in techniques that require evidence of a reside face, slipping right into a solid virtual id like slipping into a dressing up.
When criminals mix biometric templates with different leaked information, similar to logins for social media profiles or house addresses, they are able to construct “super-profiles” attached to lots of an individual’s actions. For the reason that face acts as an everlasting linking key, this point of id robbery is tricky to opposite.
Learn how to reduce the risk
Persons are nonetheless understanding easy methods to reside with fashionable biometric assortment. The ease of easily passing safety assessments or making purchases is interesting, however it incessantly comes with an everlasting chance to privateness and safety.
To minimize the risk, organizations can observe a number of information privateness very best practices. They may be able to stay handiest knowledge this is essential, erase the remaining temporarily and encrypt each mathematical template. They may be able to retailer handiest encrypted templates fairly than uncooked footage. They may be able to use safeguarding tactics, similar to the newest liveness detection tactics, to lend a hand be sure that their techniques are interacting with actual folks fairly than pictures, mask or deepfakes. And they are able to undertake a privacy-by-design manner, this means that they’re going to stay information handiest so long as essential, obviously record the way it’s used and prohibit who has get right of entry to.
Shoppers can take steps as neatly. In puts with privateness regulations, similar to California, Illinois and the Ecu Union, folks can publish an information get right of entry to request to peer what biometric information an organization holds and, in some instances, ask for its deletion. They may be able to additionally ask outlets any place what information is gathered, how lengthy it’s saved and the way it’s secure.





